
Introduction to Self-Sovereign Identity Components – Part 1
Self-Sovereign Identity (SSI) is increasingly mentioned in connection with innovations and digital identities. Even in the context of the coronavirus crisis, SSI finds possible applications, such as the possible use of a tracking app for infected people or as a digital staff “passport” in hospitals that respects each user’s privacy. To support others in classifying SSI correctly, we are now publishing a series of blog posts that explain components of SSI. The first part of the introduction to Self-Sovereign Identity focuses on the three essential components – DIDs, DID Documents and Verifiable Credentials.
As already described in detail in the first blog post, Self-Sovereign Identity offers the user the possibility to manage their own digital identities completely autonomously. There is no platform or provider, such as an email address provider or a social network that controls identity. This is achieved using an underlying blockchain or a DLT on which key pairs can easily be generated that serve as identity representation.
Decentralized Identifiers
Now we come to the first component – the Decentralized Identifiers (DIDs). Their purpose is to act as a unique identifier of the person or object. These are derived from the public keys and can be identified over various blockchains. An example DID is shown below.
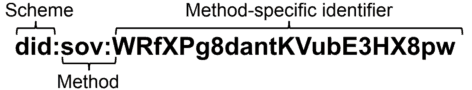
DIDs follow a general syntax: the schema (did:), the method (sov:) and the method-specific identifier (WRfXPg8dantKVubE3HX8pw). While the scheme is always the same, the method that describes how a DID is derived from a blockchain (here: Sovrin) and the method-specific identifier bo depend on the underlying blockchain. However, DIDs alone don’t bring any value.
DID Document
What fills a DID with life is the DID Document. This piece of data describes the DID object and its properties. By default, it contains the associated public key to a DID. However, it is also possible to add more public keys to the DID document that are authorized to perform actions in the name of a DID. Moreover, a DID can contain different types of attributes and service endpoints that allow the actual interaction with a DID. Changes to a DID Document can only be made by authorized public keys defined in the DID Document. An example DID Document with authorized public keys.
Verifiable Credentials
Now, that it is possible to identify an entity and to interact with it, is possible to attach information to the digital identity. This can be done with Verifiable Credentials (VCs) that act as an attestation or a digital representation of a credential such as an ID, a driver’s license or a club membership card. A VC consists of three main values:
- The issuer’s DID and signature
- The entity’s DID
- The information that is attached
Based on these three fragments, third-party verifiers can immediately determine the authenticity of the object by looking up the issuer’s DID. Verifiable Credentials are in possession of the DID owner that it was issued to and can be stored in a wallet. However, the issuer can always revoke the VC and adding it to the revocation registry that should be publicly visible.
These three components serve as the basis for a decentralized, trustless identity ecosystem that doesn’t rely on centralized authorities. DIDs identify an identity over, the DID Document describes the DID and a Verifiable Credential attaches verifiable information to a DID. Users are in sole control of their identity and can decide how information is shared and with whom.
However, this was only a small part of the entire SSI infrastructure. Part 2 of the Introduction to Self-Sovereign Identity components is about DID resolution, the process of resolving a DID Document from the DID, and DID authentication.
This post was originally published on Datarella by Martin Schäffner
No Comments